PfSense: различия между версиями
Sol (обсуждение | вклад) |
Sol (обсуждение | вклад) |
||
| (не показана 1 промежуточная версия этого же участника) | |||
| Строка 57: | Строка 57: | ||
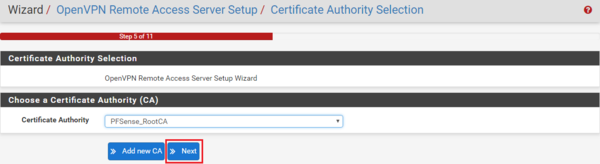
Next Select the Certificate Authority and click '''Next'''. If you have not created one, follow the steps above. | Next Select the Certificate Authority and click '''Next'''. If you have not created one, follow the steps above. | ||
| − | [[Файл:PFSense | + | [[Файл:PFSense OpenVPN09.png|600px|none|none]] |
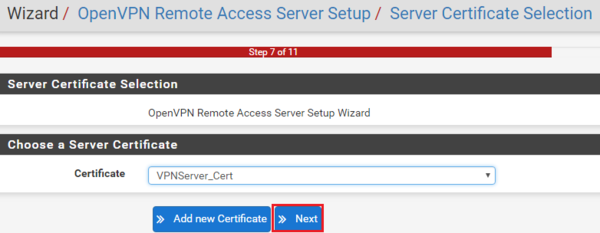
The next step is to select the VPN Server Certificate. Once completed click '''Next'''. Again, if you have not created one, follow the steps above. | The next step is to select the VPN Server Certificate. Once completed click '''Next'''. Again, if you have not created one, follow the steps above. | ||
| Строка 92: | Строка 92: | ||
[[Файл:PFSense OpenVPN15.png|800px|none|none]] | [[Файл:PFSense OpenVPN15.png|800px|none|none]] | ||
| + | |||
| + | === Installing the OpenVPN Client Export Package === | ||
== routing between IPsec and openVPN tunnels == | == routing between IPsec and openVPN tunnels == | ||
Текущая версия на 12:26, 19 января 2021
IPsec duble 2 phase (split connections)
(IKEv2 Only) When an IKEv2 tunnel has multiple Phase 2 definitions, by default the settings are collapsed in the IPsec configuration such that all P2 combinations are held in a single child SA.
Split Connections changes this behavior to be more like IKEv1 where each P2 is its configured by the daemon as own separate child SA.
Certain scenarios require this behavior, such as:
- The remote peer does not properly handle multiple addresses in single traffic selectors. This is especially common in Cisco equipment.
- Each child SA must have unique traffic selector or proposal settings. This could be due to the peer only allowing specific combinations of local/remote subnet pairs or different encryption options for each child SA.
Setting Up OpenVPN on PFSense 2.4.
Creating the Certificate Infrastructure needed for PFSense and OpenVPN
OpenVPN uses certificates to secure the VPN service for authentication and encryption purposes. The first thing we need to do on PFSense is create a Certificate Authority. If you already have one configured you can skip this step.
Creating a Certificate Authority on PFSense
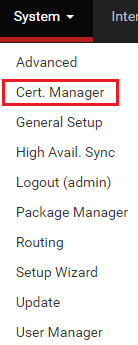
The first step in the process is to navigate to the built-in PFSense Certificate Manager
You will then be presented with a dashboard detailing the list of CA’s installed on the server. In the example below there isn’t one so click on +Add to create a new one.
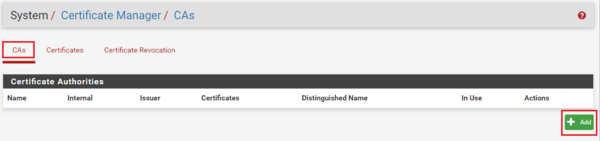
Next we need to fill out the form which PFSense will use to create the Certificate Authority. Since we are building an Internal Certificate Authority, select this option from the drop-down list as highlighted in the image below and then fill out the necessary details about your organization in the fields provided. Remember to give you CA a useful common name which you can use to identify it. In my example I used PFSense_RootCA. Once done, click on Save and your Internal Certificate Authority will be created.
Creating the OpenVPN Server Certificate on PFSense
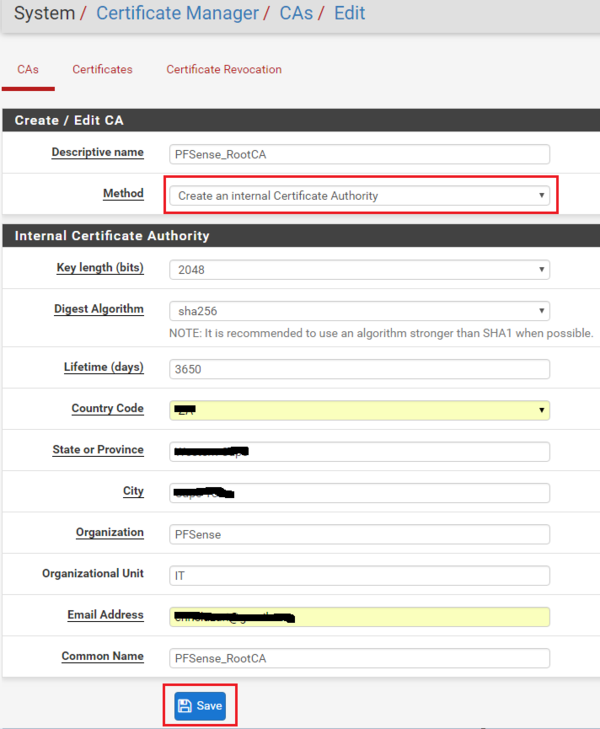
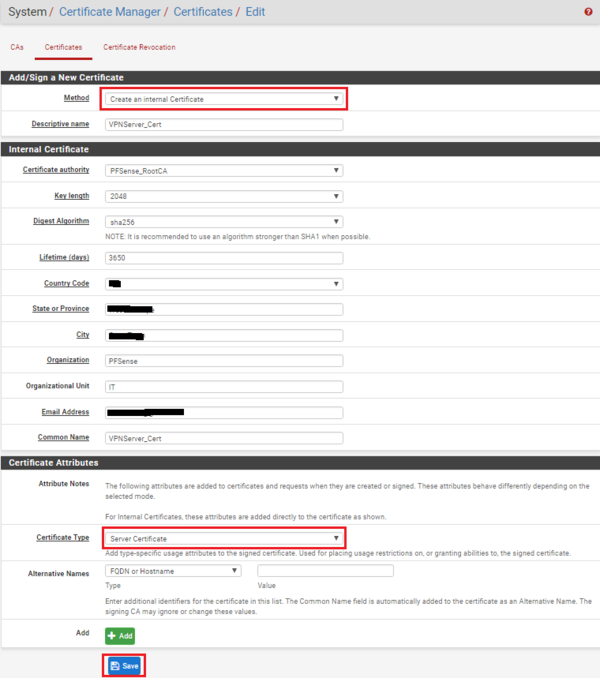
The next step is to create the certificate for the OpenVPN server which clients will use to verify the identity of the server when connecting to it. Under System – Certificate Manager navigate to the Certificates tab and click on + Add/Sign.
Next complete the form to create the certificate. Note you need to select the Create an internal Certificate method and ensure you select Server Certificate as the certificate type. Fill in the rest of the relevant information and once complete, click on Save.
The certificate infrastructure needed for OpenVPN is now complete so we can move onto the next phase, creating the OpenVPN service
Configuring OpenVPN on PFSense
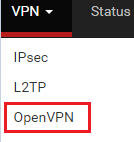
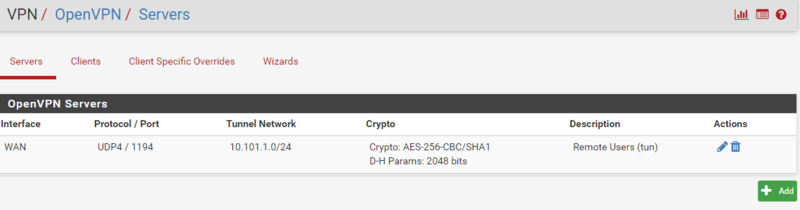
We will be using the OpenVPN configuration wizard for this step. To start go to VPN in the main menu and then click on OpenVPN.
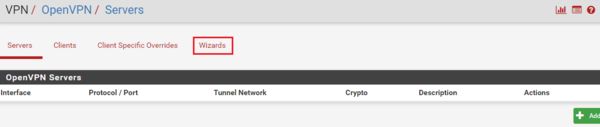
Next click on the Wizards tab to start the configuration sequence.
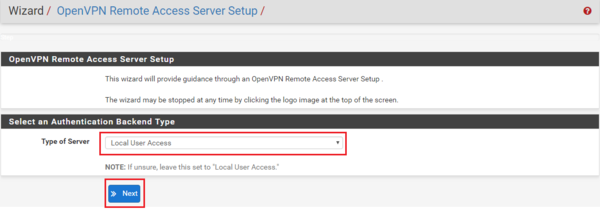
We now need to select type of server. In the drop-down list provided, select Local User Access and then click Next
Next Select the Certificate Authority and click Next. If you have not created one, follow the steps above.
The next step is to select the VPN Server Certificate. Once completed click Next. Again, if you have not created one, follow the steps above.
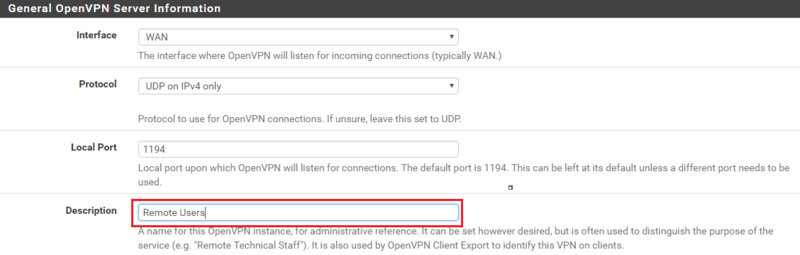
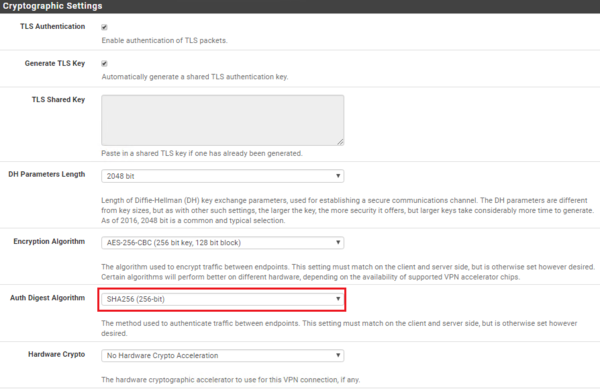
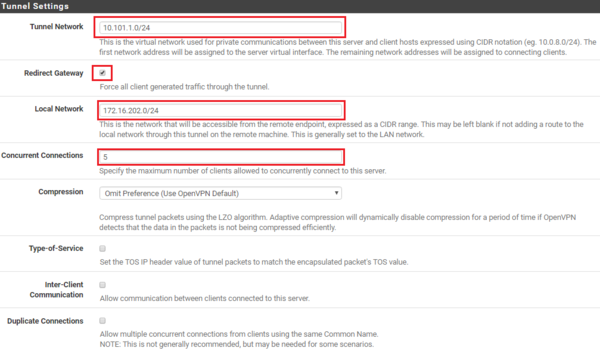
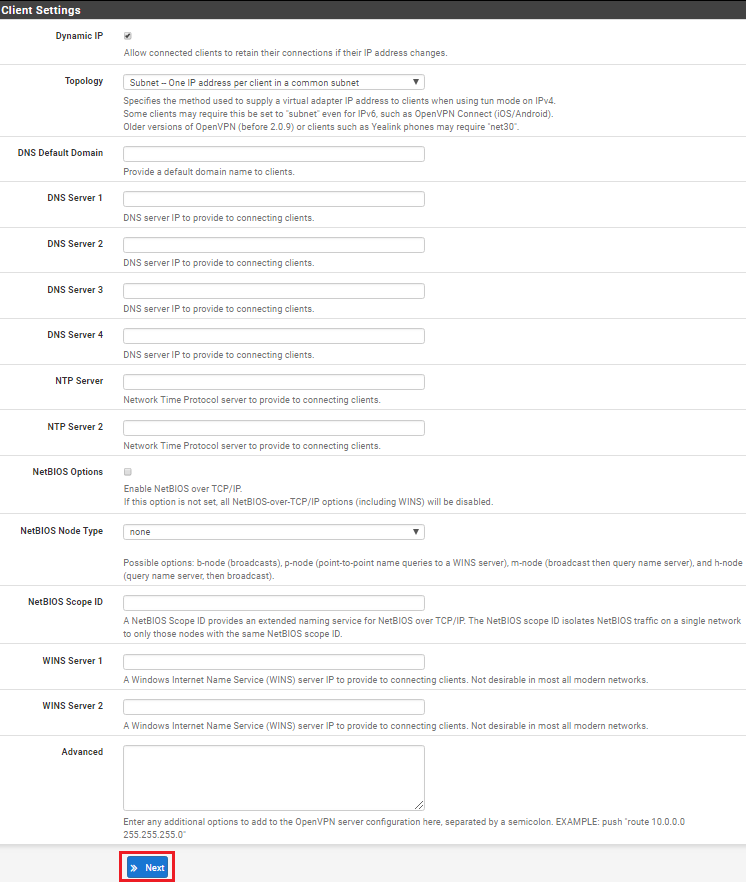
Next you will need to complete the Server Setup form which consists of four sections: General OpenVPN Server Information, Cryptographic Settings, Tunnel Settings and Client Settings. As each environment is different, you may need to adjust these to meet your specific requirements. The settings below are the default settings which ensure privacy and use PFSense as your DNS server etc.
First, let’s configure the General OpenVPN Server Information. Leave everything as default and give your VPN a description if you so choose as per the example below.
Under Cryptographic Settings, leave everything as default but change the Auth Digest Algorithm to SHA256 as per the example below since SHA1 is not that secure.
Under Tunnel Settings, enter the IP address range in CIDR notation for the Tunnel network (this will be the IP address range OpenVPN will use to assign IP’s to VPN clients). You also need to tick the checkbox labeled Redirect Gateway to ensure all clients only use the VPN for all their traffic. Next enter the local network IP address range in CIDR notation (this is usually your LAN) and then set your maximum number of concurrent connections.
In my configuration example I have left all Client Settings in their default state. Here you may want to specify a DNS server etc. Once completed click on Next.
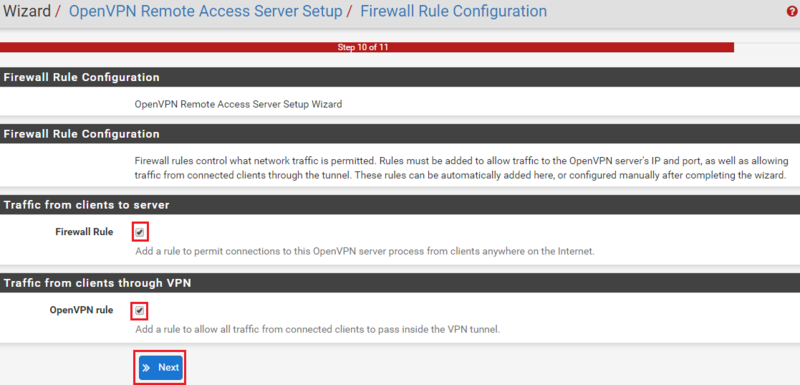
Next the wizard will want to create the Firewall rule configuration. Select the Firewall rule and the OpenVPN rule as per the example below and click Next
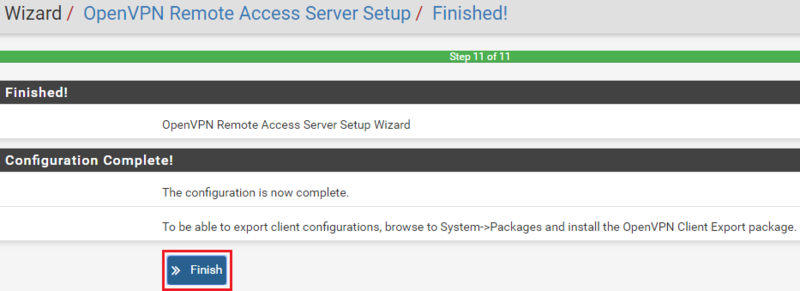
Finally, the configuration is complete. Click Finish.
You should now have a configured OpenVPN server, a newly created WAN Firewall Rule and an OpenVPN tab under Firewall rules with the OpenVPN rule configured. Examples below.